Introduction
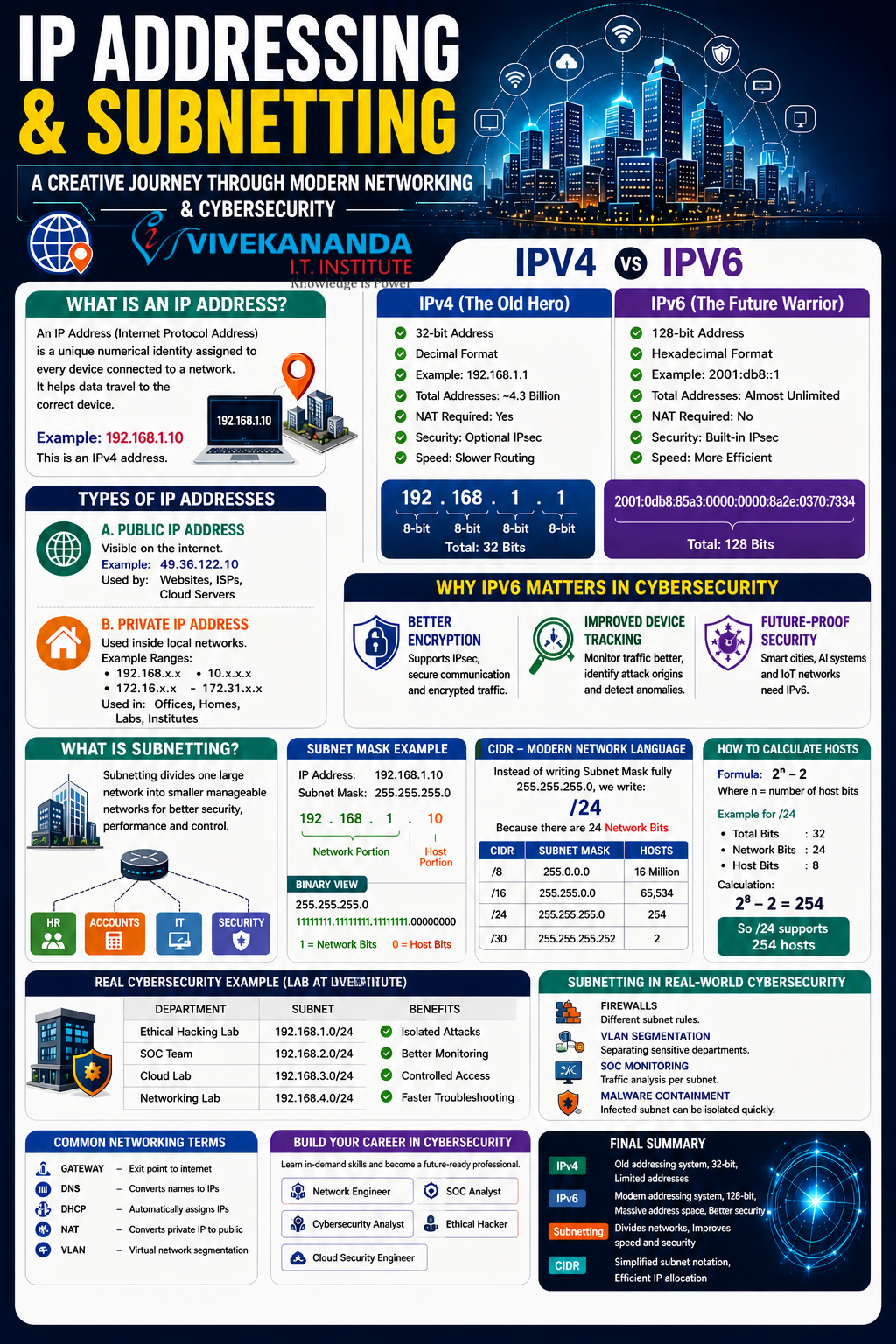
In today’s digital world, networking and cybersecurity form the backbone of communication. Every device connected to the internet relies on a structured system to send and receive data efficiently. This system is built on IP addressing and subnetting.
Understanding these concepts is essential for anyone pursuing a career in networking, ethical hacking, or cybersecurity.
Imagine the Internet as a Smart City
Think of the internet as a massive smart city:
- Every house = a device
- Every street = a network
- Every citizen = data packets
- Every address = an IP address
Without proper addressing, data would never reach the correct destination. This is where IP addressing plays a crucial role.
What is an IP Address?
An IP Address (Internet Protocol Address) is a unique numerical label assigned to each device connected to a network.
Just like a home address helps deliver parcels, an IP address ensures data reaches the right device.
Example (IPv4):
192.168.1.10
Types of IP Addresses
1. Public IP Address
- Visible on the internet
- Assigned by Internet Service Providers (ISPs)
- Used by websites, servers, and cloud platforms
Example: 49.36.122.10
2. Private IP Address
- Used within local networks
- Not accessible directly from the internet
Common Ranges:
- 192.168.x.x
- 10.x.x.x
- 172.16.x.x – 172.31.x.x
Used in homes, offices, and training labs.
IPv4 — The Foundation of Networking
What is IPv4?
IPv4 (Internet Protocol Version 4) is the most widely used addressing system.
Key Features:
- 32-bit address
- Divided into 4 octets
- Decimal format
Example:
192.168.10.25
Each octet ranges from 0 to 255.
Structure of IPv4
192 . 168 . 10 . 25
(8 bits each = total 32 bits)
Problem with IPv4
IPv4 provides about 4.3 billion addresses.
However, with the rise of:
- Smartphones
- IoT devices
- Cloud computing
- Smart TVs
- Security systems
The number of available IPv4 addresses is no longer sufficient.
IPv6 — The Future of Networking
What is IPv6?
IPv6 (Internet Protocol Version 6) was introduced to overcome IPv4 limitations.
Key Features:
- 128-bit address
- Written in hexadecimal format
- Nearly unlimited addresses
Example:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
IPv4 vs IPv6 Comparison
| Feature | IPv4 | IPv6 |
|---|---|---|
| Address Size | 32-bit | 128-bit |
| Format | Decimal | Hexadecimal |
| Addresses | ~4.3 Billion | Almost Unlimited |
| Security | Optional | Built-in (IPsec) |
| NAT | Required | Not Required |
| Configuration | Manual/DHCP | Auto Configuration |
Why IPv6 is Important in Cybersecurity
1. Better Security
- Built-in IPsec encryption
- Secure communication
2. Improved Monitoring
- Easier traffic tracking
- Better attack detection
3. Future-Ready
- Supports IoT, AI, and smart cities
What is Subnetting?
Subnetting is the process of dividing a large network into smaller, manageable networks.
Real-Life Example
Imagine a company with one large office room. It becomes:
- Noisy
- Hard to manage
- Less secure
So the company divides it into departments:
- HR
- Accounts
- IT
- Security
This division is called subnetting.
Why Subnetting is Important
1. Better Security
Limits unauthorized access between networks.
2. Reduced Traffic
Minimizes unnecessary data broadcasts.
3. Faster Performance
Smaller networks improve speed.
4. Easy Management
Simplifies troubleshooting and monitoring.
Understanding Subnet Mask
A subnet mask separates:
- Network portion
- Host portion
Example:
- IP Address: 192.168.1.10
- Subnet Mask: 255.255.255.0
Result:
- Network: 192.168.1
- Host: 10
Binary Representation
Subnet masks in binary:
255.255.255.0
= 11111111.11111111.11111111.00000000
- 1 = Network bits
- 0 = Host bits
CIDR — Simplified Notation
CIDR (Classless Inter-Domain Routing) simplifies subnet masks.
Example:
- 255.255.255.0 = /24
This means 24 bits are used for the network.
CIDR Examples
| CIDR | Subnet Mask | Hosts |
|---|---|---|
| /8 | 255.0.0.0 | 16 Million |
| /16 | 255.255.0.0 | 65,534 |
| /24 | 255.255.255.0 | 254 |
| /30 | 255.255.255.252 | 2 |
How to Calculate Hosts
Formula:
2ⁿ − 2
Where n = number of host bits
Example (/24):
- Host bits = 8
- 2⁸ − 2 = 254 hosts
Real Cybersecurity Example
In a cybersecurity lab, subnetting can be used like this:
| Department | Subnet |
|---|---|
| Ethical Hacking | 192.168.1.0/24 |
| SOC Team | 192.168.2.0/24 |
| Cloud Lab | 192.168.3.0/24 |
Benefits
- Attack isolation
- Better monitoring
- Controlled access
- Faster troubleshooting
Subnetting in Real-World Cybersecurity
Used in:
- Firewalls (different subnet rules)
- VLAN segmentation
- SOC monitoring
- Malware containment
Common Networking Terms
| Term | Meaning |
|---|---|
| Gateway | Exit point to the internet |
| DNS | Converts domain names to IPs |
| DHCP | Assigns IPs automatically |
| NAT | Converts private IP to public |
| VLAN | Virtual network segmentation |
Career Opportunities in Networking & Cybersecurity
Learning IP addressing and subnetting opens doors to careers such as:
- Network Engineer
- Cybersecurity Analyst
- SOC Analyst
- Ethical Hacker
- Cloud Security Engineer
Conclusion
IP addressing and subnetting are fundamental to modern networking and cybersecurity.
Without them:
- Communication would fail
- Security would collapse
- Data routing would become impossible
Mastering:
- IPv4
- IPv6
- CIDR
- Subnetting
is essential for building a successful IT career.









