Routers vs switches & VLAN fundamentals
Routing and Switching Basics | The Backbone of Modern Networking
In today’s digital world, every email, video call, online transaction, and cloud application depends on a strong and secure network. Behind this seamless communication are two powerful networking technologies:
Routing and Switching. These technologies form the foundation of every modern IT infrastructure and play a critical role in the field of cybersecurity.
At Vivekananda IT Institute, students learn networking concepts through practical labs, real-world examples and cybersecurity focused training that prepares them for modern IT careers.
- What is Routing?
Routing is the process of transferring data packets from one network to another using a device called a router.
Imagine the internet as a giant highway system. A router works like an intelligent traffic controller that decides the best path for data to travel from source to destination.
- For example:
- Your laptop in Vadodara sends a request to open a website.
- The request passes through multiple routers across cities and countries.
- Routers security destination IP addresses and forward data through the best available path.
Without routing, communication between different networks would be impossible.
- What is Switching?
Switching is the process of forwarding data within the same local network using a switch.
Think of a switch as the smart manager inside an office building. It ensures that data reaches the correct device without disturbing others.
- For example:
- In a computer lab at a cybersecurity institute,
- Multiple systems are connected to a switch,
- The switch sends data only to the intended computer,
- This improves speed, efficiency, and security.
- Switches are commonly used in:
- Offices
- Schools
- Cybersecurity labs
- Data hubs
- IT institutes
At Vivekananda IT Institute, students gain hands-on experience configuring switches and routers to understand real networking environments.
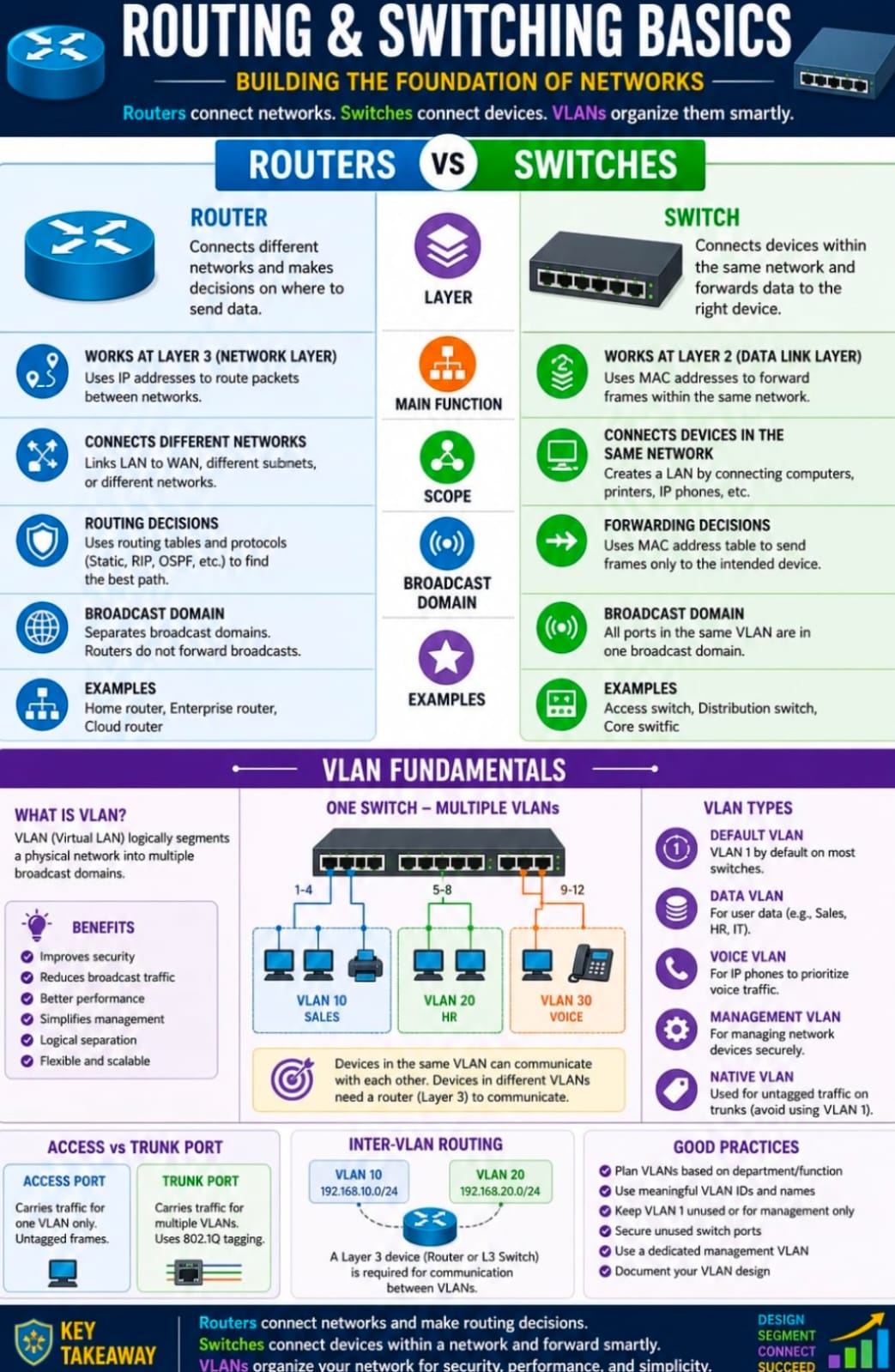
- Routers vs Switches
Although routers and switches are both networking devices, their functions are very different.
| Feature | Router | Switch |
| Purpose | Connects different networks | Connects devices within same network |
| Works On | IP Address | MAC Address |
| OSI Layer | Layer 3 (Network Layer) | Layer 2 (Data Link Layer) |
| Traffic Control | Routes packets between networks | Forwards frames inside LAN |
| Internet Access | Provides internet connectivity | Does not directly provide internet |
| Security Features | Firewall, NAT, ACL | VLAN, Port Security |
| Example | Home Wi-Fi Router / Industrial Routers | Office LAN Switch / Manageable switch |
- How Routers Work
Routers use routing tables to determine the best path for data transmission.
- The router performs these tasks:
- Reads destination IP address
- Checks routing table
- Finds best route
- Forwards packet to next network
- Routers can use:
- Static Routing
- Dynamic Routing
- Default Routing
- Modern enterprise routers also include:
- Firewall protection
- VPN support
- Traffic filtering
- Intrusion prevention
These features make routers important in cybersecurity infrastructures.
- How Switches Work
A switch learns the MAC addresses of connected devices and stores them in a MAC address table.
- When data arrives:
- Switch checks destination MAC address
- Finds matching port
- Sends data only to that device
- Benefits of switches:
- Faster communication
- Reduced collisions
- Better bandwidth utilization
- Improved LAN performance
Managed switches also provide advanced security and monitoring features.
- Understanding VLAN Fundamentals
A VLAN (Virtual Local Area Network) is a technology that divides one physical network into multiple logical networks.
- Imagine a large IT institute in Vadodara where:
- Faculty systems
- Student systems
- Admin systems
- Cybersecurity labs
all use the same switch infrastructure.
Without VLANs, all devices communicate in one large network, creating:
- Congestion
- Security risks
- Broadcast traffic overload
Using VLANs, the network can be separated logically.
- Example:
| VLAN ID | Department | |
| VLAN 10 | Administration | |
| VLAN 20 | Faculty | |
| VLAN 30 | Students | |
| VLAN 40 | Cybersecurity Lab |
This improves:
- Network performance
- Security
- Traffic management
- Access control
At Vivekananda IT Institute, students learn how VLANs are configured in real enterprise environments to secure organizational networks.
- Benefits of VLANs in Cybersecurity
VLANs are extremely important in cybersecurity because they isolate sensitive systems from general users.
1. Enhanced Security
Sensitive departments can be separated from public networks.
Example:
- Finance systems stay isolated from student systems.
2. Reduced Broadcast Traffic
Broadcast traffic remains inside its VLAN, improving speed and efficiency.
3. Better Network Management
Administrators can organize networks easily based on departments or projects.
4. Improved Performance
Smaller broadcast domains reduce unnecessary traffic.
5. Controlled Access
Security teams can apply different rules to different VLANs.
- Types of VLANs
1. Default VLAN
Every switch port belongs to the default VLAN initially.
2. Data VLAN
Used for normal user-generated traffic.
3. Voice VLAN
Dedicated to VoIP communication.
4. Management VLAN
Used for remote switch management.
5. Native VLAN
Handles untagged traffic on trunk ports.
- VLAN Tagging and Trunking
When VLAN traffic moves between switches, special techniques are used.
- VLAN Tagging
Adds VLAN information to Ethernet frames.
- Common protocol:
- IEEE 802.1Q
- Trunk Port
A trunk port carries traffic from multiple VLANs between switches.
- Access Port
An access port belongs to a single VLAN.
- Routing Between VLANs
Devices in different VLANs cannot communicate directly.
To enable communication, a router or Layer 3 switch performs:
- Inter-VLAN Routing
Example:
- Student VLAN communicates with server VLAN securely.
This concept is widely used in:
- Banks
- Corporate offices
- Universities
- Cybersecurity institutes
Importance of Routing and Switching in Cybersecurity
Modern cybersecurity depends heavily on proper network architecture.
Routing and switching help organizations:
- Segment networks
- Control access
- Detect attacks
- Prevent unauthorized communication
- Monitor suspicious traffic
Cybersecurity professionals use these concepts for:
- Network security
- Penetration testing
- Firewall implementation
- Secure architecture design
- Threat monitoring
- Real-World Example
- Imagine a cybersecurity training hub in Vadodara:
- Students practice ethical hacking
- Security labs run malware simulations
- Faculty systems contain confidential data
- Using VLANs and routers:
- Labs remain isolated
- Malware cannot spread easily
- Sensitive systems stay protected
- Network performance remains stable
This is why practical routing and switching knowledge is essential for every cybersecurity professional.
At Vivekananda IT Institute, students receive industry-oriented training in routing, switching, VLAN configuration, and cybersecurity networking technologies that help them build successful IT careers.
Conclusion
Routing and switching are the heart of modern networking. Routers connect different networks, while switches manage communication within local networks. VLANs further improve security and efficiency by dividing networks into logical segments.
For anyone interested in networking or cybersecurity, understanding these concepts is the first step toward becoming a skilled IT professional.
Whether you dream of becoming a Network Engineer, Security Analyst, Ethical Hacker, or System Administrator, mastering routing and switching fundamentals is essential in today’s digital world.
Students at Vivekananda IT Institute in Vadodara gain practical exposure to these technologies through hands-on labs, expert guidance, and real-world cybersecurity scenarios.









