Cryptography and Encryption: The Digital Shield of Cybersecurity
In today’s connected world, every message, online payment, email, and login travels through networks. The answer lies in Cryptography and Encryption the backbone of modern cybersecurity.
At Vivekananda IT Institute, Vadodara, students learning networking and cybersecurity are introduced to the powerful concepts of cryptography that secure digital communication across the globe. Whether it’s protecting banking transactions, securing passwords, or defending corporate networks, cryptography plays a critical role in modern IT infrastructure.
- What is Cryptography?
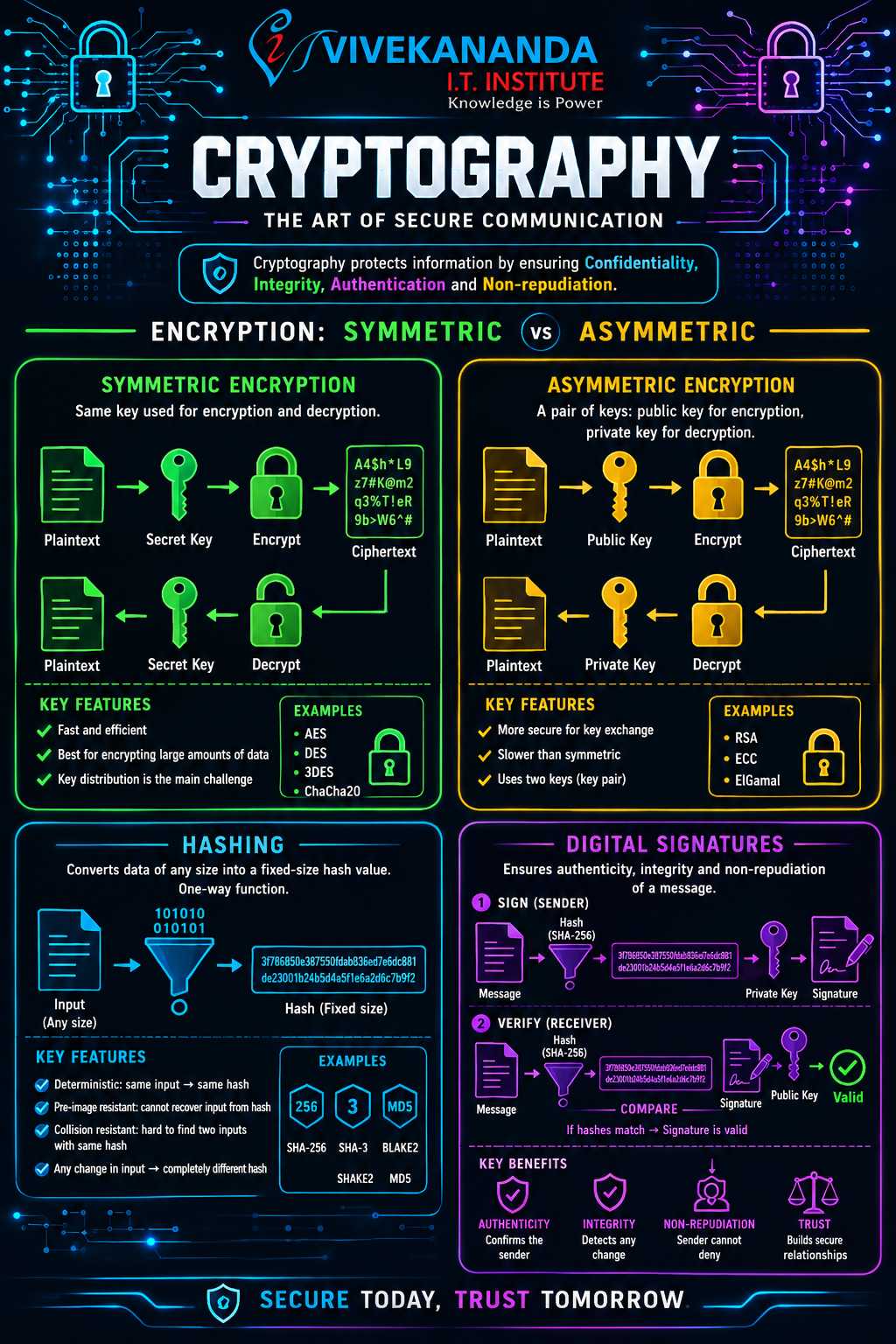
Cryptography is the science of protecting information by converting readable data into an unreadable format using mathematical algorithms. Only authorized users with the correct key can access the original information.
- Imagine sending a secret letter:
- Normal text = Plaintext
- Locked secret code = Cipher text
- Locking process = Encryption
- Unlocking process = Decryption
- In networking and cybersecurity, cryptography ensures:
- Data confidentiality
- Data integrity
- User authentication
- Secure communication
At Vivekananda IT Institute in Vadodara, cybersecurity students explore how cryptography protects organizations from data breaches and cyberattacks.
- What is Encryption?
Encryption is the process of transforming readable information into encoded data that unauthorized users cannot understand.
- For example:
- Original message: Welcome to Cyber Security
- Encrypted message: X7#kP9@Lm2
Without the correct decryption key, hackers cannot read the message.
- Encryption is widely used in:
- Online banking
- VPN s
- Email security
- Wi-Fi security
- Cloud storage
- E-commerce websites
Types of Encryption
- There are two major types of encryption:
- Symmetric Encryption
- Asymmetric Encryption
Symmetric Encryption
Symmetric encryption uses one single key for both encryption and decryption.
If User A encrypts a file using a secret key, User B must use the same key to decrypt it.
- How Symmetric Encryption Works?
- Sender encrypts data using a secret key.
- Encrypted data travels across the network.
- Receiver uses the same key to decrypt the data.
- Example
Plaintext → Encryption Key → Cipher text
Cipher text → Same Key → Plaintext
- Popular Symmetric Algorithms
- AES (Advanced Encryption Standard)
- DES (Data Encryption Standard)
- 3DES
- Blowfish
Advantages of Symmetric Encryption
- Faster Performance
Symmetric encryption works very quickly, making it ideal for large amounts of data.
- Less Resource Usage
It requires lower computational power.
Efficient for Real-Time Communication
- Used in:
- VPN tunnels
- Wi-Fi encryption
- Secure file transfer
Disadvantages of Symmetric Encryption
- Key Sharing Problem
The biggest challenge is securely sharing the secret key.
- Scalability Issues
Managing keys becomes difficult in large organizations.
Real-World Example of Symmetric Encryption
When you connect to secure Wi-Fi using WPA2 or WPA3, symmetric encryption protects the communication between your device and the router.
Students at Vivekananda IT Institute, Vadodara learn how symmetric encryption is implemented in enterprise networks and wireless security systems.
Asymmetric Encryption
- Asymmetric encryption uses two different keys:
- Public Key
- Private Key
One key encrypts the data, while the other decrypts it.
- How Asymmetric Encryption Works?
- Receiver creates:
- Public Key
- Private Key
- Public key is shared openly.
- Sender encrypts data using the public key.
- Only the receiver’s private key can decrypt the message.
- Example of Asymmetric Encryption
Public Key → Encrypt Data
Private Key → Decrypt Data
- Popular Asymmetric Algorithms
- RSA
- ECC (Elliptic Curve Cryptography)
- Diffie-Hellman
- DSA
Advantages of Asymmetric Encryption
- Better Security
Private keys are never shared publicly.
- Secure Key Exchange
Solves the key distribution problem found in symmetric encryption.
- Digital Authentication
Supports digital signatures and certificates.
Disadvantages of Asymmetric Encryption
- Slower Speed
Requires more computational power.
- Complex Implementation
More difficult to configure and manage.
Real-World Use of Asymmetric Encryption
Asymmetric encryption is used in:
- HTTPS websites
- SSL/TLS certificates
- Secure emails
- Online banking
- Cryptocurrency systems
Whenever you see a padlock icon in a browser, asymmetric encryption is helping secure the connection.
At Vivekananda IT Institute in Vadodara, students practice configuring SSL certificates and understanding public-key infrastructure (PKI).
Symmetric vs Asymmetric Encryption
| Feature | Symmetric Encryption | Asymmetric Encryption |
| Keys Used | One Key | Two Keys |
| Speed | Faster | Slower |
| Security | Moderate | High |
| Key Sharing | Difficult | Easier |
| Best For | Bulk Data Encryption | Secure Communication |
| Examples | AES, DES | RSA, ECC |
What is Hashing?
Hashing is a process that converts data into a fixed-length value called a hash.
- Unlike encryption:
- Hashing cannot be reversed.
- It is a one-way process.
Example of Hashing
Password → Hash Function → Hashed Output
Even a tiny change in data creates a completely different hash value.
Common Hashing Algorithms
- MD5
- SHA-1
- SHA-256
- SHA-512
Uses of Hashing in Cybersecurity
- Password Protection
Websites store hashed passwords instead of plain passwords.
- File Integrity Verification
Hashing detects whether files were modified.
- Block chain Technology
Cryptocurrencies use hashing extensively.
- Digital Forensics
Investigators verify data authenticity using hashes.
Students at Vivekananda IT Institute, Vadodara gain practical exposure to password security and hashing techniques used in ethical hacking.
What are Digital Signatures?
- Digital signatures verify:
- Identity of the sender
- Authenticity of data
- Integrity of communication
- Digital signatures combine:
- Hashing
- Asymmetric encryption
How Digital Signatures Work?
- Original message is hashed.
- Hash is encrypted using sender’s private key.
- Receiver decrypts using sender’s public key.
- Receiver compares hashes.
- If hashes match:
- Data is authentic
- Data was not modified
Benefits of Digital Signatures
- Authentication
Confirms sender identity.
- Integrity
Ensures data was not altered.
- Non-Repudiation
Sender cannot deny sending the message.
Real-World Applications of Digital Signatures
- Online contracts
- Government portals
- Banking systems
- Software downloads
- Secure email communication
Importance of Cryptography in Networking and Cybersecurity
Cryptography is essential for:
- Securing networks
- Protecting confidential information
- Preventing cyberattacks
- Maintaining privacy
- Enabling safe online transactions
Without cryptography:
- Passwords could be stolen easily
- Financial fraud would increase
- Online communication would become insecure
That is why cybersecurity professionals must understand encryption technologies deeply.
Learn Cybersecurity with Vivekananda IT Institute, Vadodara
As cyber threats continue to grow, skilled cybersecurity professionals are in high demand.
Vivekananda IT Institute in Vadodara provides industry-focused training in:
- Ethical hacking
- Network security
- Cryptography
- Penetration testing
- Firewall configuration
- Digital forensics
- Wireshark and Map tools
The institute combines practical labs, real-world cybersecurity scenarios, and expert guidance to help students build successful careers in networking and cybersecurity.
Conclusion
Cryptography and encryption form the foundation of secure digital communication. From protecting passwords and banking systems to securing corporate networks and cloud platforms, these technologies are essential in today’s cyber world understanding.
- Symmetric encryption
- Asymmetric encryption
- Hashing
- Digital signatures
and is crucial for every cybersecurity professional.
With advanced cybersecurity education from Vivekananda IT Institute, Vadodara, students can gain practical expertise in modern security technologies and prepare for the rapidly growing cybersecurity industry.









